Documentation Index
Fetch the complete documentation index at: https://docs.turnkey.com/llms.txt
Use this file to discover all available pages before exploring further.
What is Turnkey Verifiable Cloud (“TVC”)?
Turnkey Verifiable Cloud is a new offering to externalize the Foundations of our TEE-based key management system. With TVC, you can run any code in isolated, verifiable secure enclaves powered by Turnkey’s trusted infrastructure. Turnkey started as a key management system with a drastic threat model, and we placed a bet on TEEs early on. More specifically, Turnkey uses AWS Nitro Enclaves to deploy all sensitive workloads, and we plan to support other major cloud providers in the future. To establish the foundations for our key management system, we went deep on build systems, deployment tooling, verification tooling, provisioning, performance, and scaling. This work, developed over 3+ years, is broadly applicable. Any team building at scale within Trusted Execution Environments will encounter the same challenges. TVC solves these problems transparently for the industry at large, within and outside of web3. A few of the hard problems solved by TVC:- Reproducible builds: These are crucial to leverage remote attestations (see this blog post). To support this, we bootstrapped StageX, an open-source distro focused on reproducibility. TVC works with StageX so reproducibility is handled for you. Learn more about it here.
- Packaging: Packaging applications into EIF files is easy on the surface but leaves application developers with load-bearing security decisions: which base OS do I use? How do I handle application upgrades? How do I persist state? Turnkey built QuorumOS to solve these problems in the context of our own key management platform. TVC is integrated with QOS to handle these problems for you. In TVC, you provide the binary application you’d like to run, and we take care of the rest.
- Running at production scale: Turnkey has invested years of engineering time to get this right. We are running enclaves with autoscaling to ensure your application can transparently scale up and down with traffic. We have automated provisioning and invented key forwarding to ensure enclaves going down are automatically replaced and provisioned from already-running enclaves, Operators do not have to wake up in the middle of the night.
- Verification tooling: Turnkey is regularly audited by top security firms to guarantee verification procedures and the code implementing them remains secure and correct over time.
Use cases
Many different types of workloads can benefit from verifiability. Below is a list of use cases supported by TVC.| Workload type | Advantages to verifiability |
|---|---|
| Chain Abstraction | Trustworthy cosigners for cross-chain resource locks (e.g. OneBalance) |
| Transaction Construction | Users know that the unsigned transaction bytes are legitimate. |
| Transaction Parsing | Provide accurate metadata about the effects of a transaction. This is critical for trusted wallet UX. See VisualSign Parser. |
| Oracles | Leverage external data without the overhead of full decentralization, on-chain or off-chain. Replace economic incentives with verifiability. |
| Blockchain nodes | Allow for private balance lookups, verifiable mempool inclusion, and more. |
| Web2 data bridging | Import and use data from web2 providers (centralized exchange balances, credit scores, X follower counts) in decentralized computation |
| AI training & inference | Verifiable training to prove no hidden backdoors; guarantee user prompts remain private |
| Sequencers | Prove correct behavior and eliminate the need for challenge periods and economic incentives around them (e.g. Base sequencer) |
| Identity verification | Prove no identity is leaked as part of the verification process. |
| VPN nodes | Guarantees privacy by proving that forwarded traffic isn’t logged anywhere. |
| Exchanges | Ensure no malicious behavior (frontrunning), and create verifiable order books. |
| PII processing | Prove that processing does not leak or misuse PII (Personally Identifiable Information). |
Architecture
We’ve engineered TVC to fit within the existing Turnkey products and APIs. You will interact with TVC via our dashboard, via the TVC CLI, or programmatically via APIs. TVC provides a secure harness (QuorumOS) to verifiably run a single program. This program is also called “binary”, “executable” or sometimes “pivot”, and contains the secure workload to execute in TEEs. TVC relies on OCI container images to transport this executable program from where it’s built (typically, Github Action, or other CI platforms) to within TVC. This has several advantages:- OCI containers can be hosted on many container image registries. These registries ensure integrity of the images, and clients can “pin” an image to ensure that they download the image they expect. Typically a container image URL will look like
registry.com/org/repo:some-tag@sha256:digest. - Registries also support authentication, which means TVC supports private image registries. Our infrastructure is Kubernetes-based: we support Pull Secrets generically to allow for maximum flexibility: Docker Hub, ECR, GHCR, ACR, GAR are all supported.
Applications
TVC is programmable infrastructure, enabling you to create and manage verifiable apps. Each TVC App is deployed on Turnkey infrastructure in the exact same way as Turnkey’s own core enclave apps.- TVC Applications are deployed within Kubernetes clusters operated by Turnkey, using QuorumOS (“QOS”) as a base OS.
- Key provisioning, high-availability deployments (minimum of 3 replicas), and in-depth verification workflows are supported by default.
- Because TVC relies on Turnkey for its own operations, it’s possible to use Consensus in the context of TVC activities (with Turnkey Policies or Root Quorum)
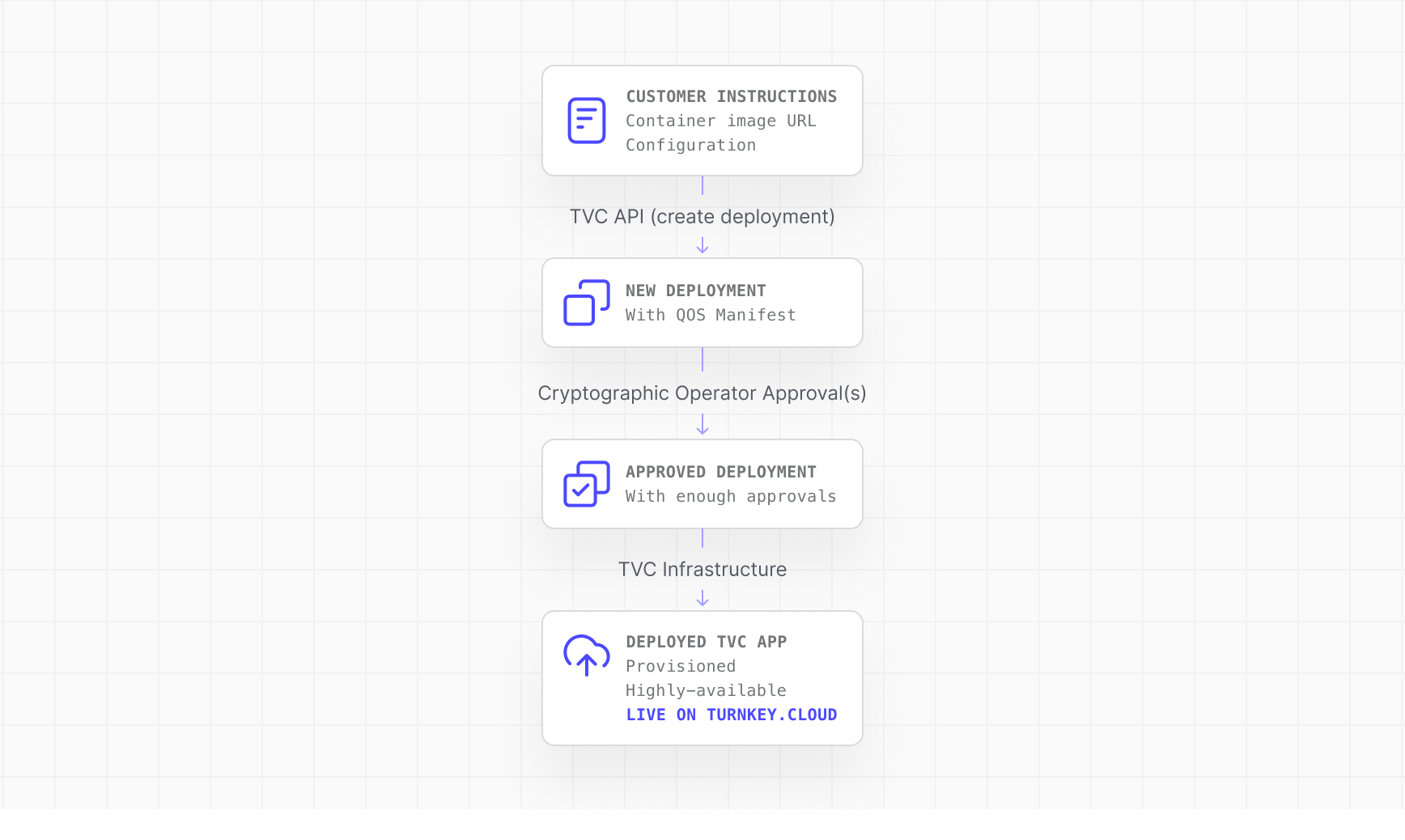
Deployments
Each TVC application can be deployed many times. For every TVC deployment, you will specify:- An OCI image URL (e.g.
ghcr.io/myorg/myrepo:tag@sha256:…). This container is pulled by our Kubernetes infrastructure. If the container is private, TVC supports uploading encrypted pull secrets. - An executable path + args: within the container, you must indicate where the desired binary lives such that Turnkey’s infrastructure can extract this binary from its OCI container, and run it within a TEE on your behalf.
- The port on which external requests should be forwarded. This is typically port 3000. For convenience TVC lets you specify different ports for user requests and health requests made by Turnkey infrastructure.
- Your expected executable digest: this is a security measure, to ensure the binary pulled by Turnkey’s infrastructure is the binary you expect.
| Resource | Default Allocation |
|---|---|
| vCPUs | 2 |
| RAM | 1 GiB |
| Filesystem | RAM-based (no persistence) |
| Replicas | 3 |
| Ingress | Load-balanced across all replicas |
| Sub-domain | Automated (<UUID>.turnkey.cloud) |
Manifests
Each TVC deployment is ultimately specified with a QOS manifest. The information you provide to TVC APIs (expected digest, executable arguments, and so on) is used to create a new QOS Manifest document. SeeManifest for a full definition of the fields within it.
This manifest document is the source of truth used by QOS to boot your application. It is also the document which must be cryptographically signed for each deployment. QOS Manifests are returned along with the AWS attestation document, within Boot Proofs. More on this in the next section.
Operators
Operators are humans or systems. In TVC, an operator is represented by an alias and a public key. Operator keys can be created and managed externally via our TVC CLI, or managed via Turnkey’s own key management APIs. QuorumOS uses operators to cryptographically control deployments: operators must approve QOS manifests and take part in deployments where Quorum Keys must be injected.Keys, Signatures, and Verification
Your TVC app has access to two keys when it boots:- Ephemeral Key: a key which is created at boot. This key never leaves the enclave and is different for every enclave. A signature by this key is a signature bound to a particular enclave, hence bound to a particular code version of your TVC application.
- Quorum Key: a key which is injected at boot and is the same across all enclaves. This key can be used to encrypt state which needs to survive application upgrades. Internally at Turnkey we use this key to sign or encrypt long-lived data.
Pricing
TVC pricing has two components:- A fixed per-month platform fee.
- Variable pricing based on wall-clock enclave uptime