Documentation Index
Fetch the complete documentation index at: https://docs.turnkey.com/llms.txt
Use this file to discover all available pages before exploring further.
Email Recovery is a legacy flow, now superseded by Email Auth, which can used to implement recovery flows and more.
Prerequisites
Make sure you have set up your primary Turnkey organization with at least one API user that can programmatically initiate email recovery on behalf of suborgs. Check out our Quickstart guide if you need help getting started. To allow an API user to initiate email recovery, you’ll need the following policy in your main organization:Helper packages
- We have released open-source code to create target encryption keys, decrypt recovery credentials, and sign Turnkey activities. We’ve deployed this a static HTML page hosted on
recovery.turnkey.commeant to be embedded as an iframe element (see the code here). This ensures the recovery credentials are encrypted to keys that your organization doesn’t have access to (because they live in the iframe, on a separate domain) - We have also built a package to help you insert this iframe and interact with it in the context of email recovery:
@turnkey/iframe-stamper
Email recovery step-by-step
Here’s a diagram summarizing the email recovery flow step-by-step (direct link):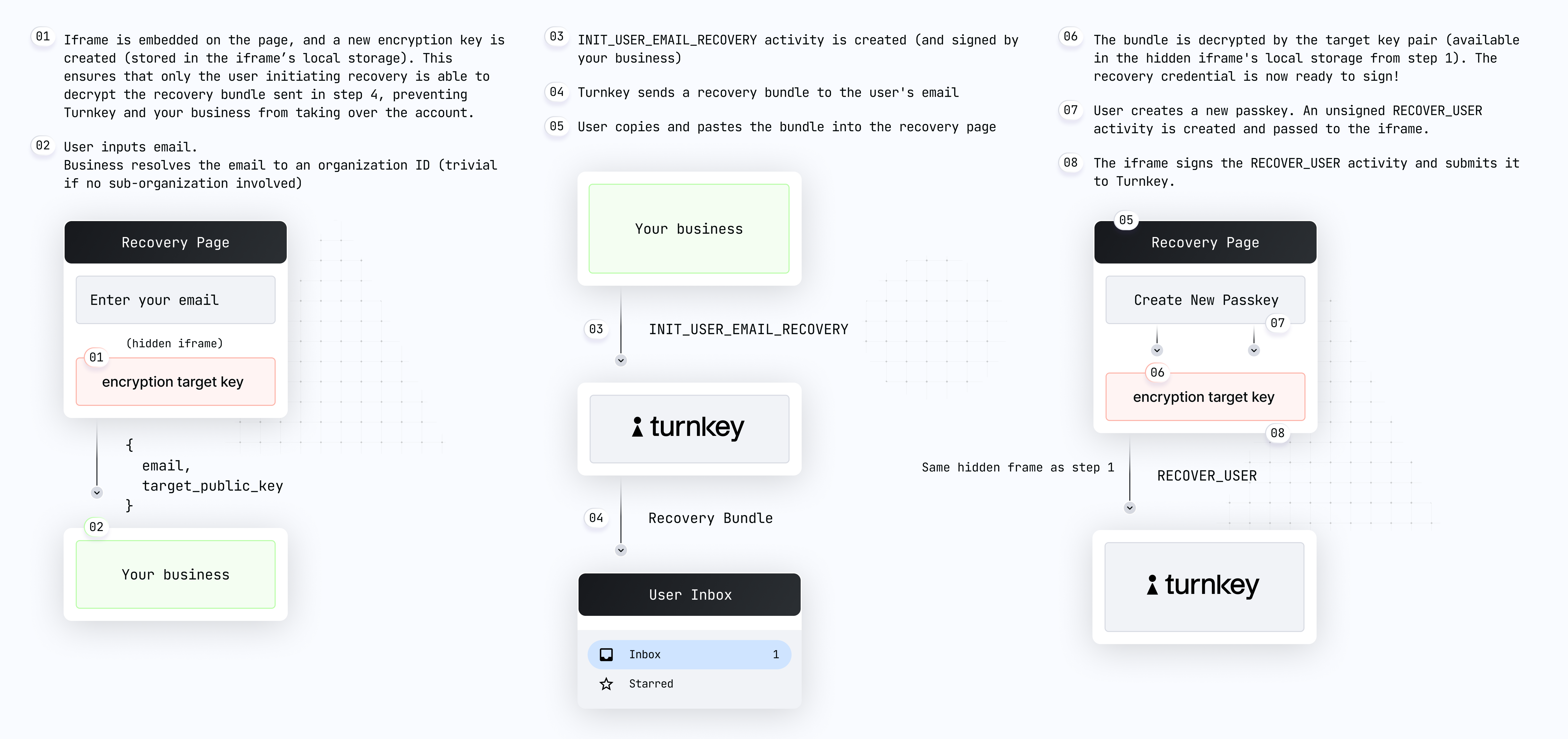
User on
yoursite.xyz clicks “recovery”, and a new recovery UI is shown. We recommend this recovery UI be a new hosted page of your site or application, which contains language explaining to the user what steps they will need to take next to complete recovery. While the UI is in a loading state your frontend uses @turnkey/iframe-stamper to insert a new iframe element:Your code receives the iframe public key and shows the recovery form, and the user enters their email address.
Your app can now create and sign a new
INIT_USER_EMAIL_RECOVERY activity with the user email and the iframe public key in the parameters. Note: you’ll need to retrieve the sub-organization ID based on the user email.User copies and pastes their recovery code into your app. Remember: this code is an encrypted credential which can only be decrypted within the iframe.
Your app uses Once the
@turnkey/iframe-stamper to sign a new RECOVER_USER activity:RECOVER_USER activity is successfully posted, the recovery is complete! If this activity succeeds, your frontend can redirect to login/sign-in or perform crypto signing with the new passkey.