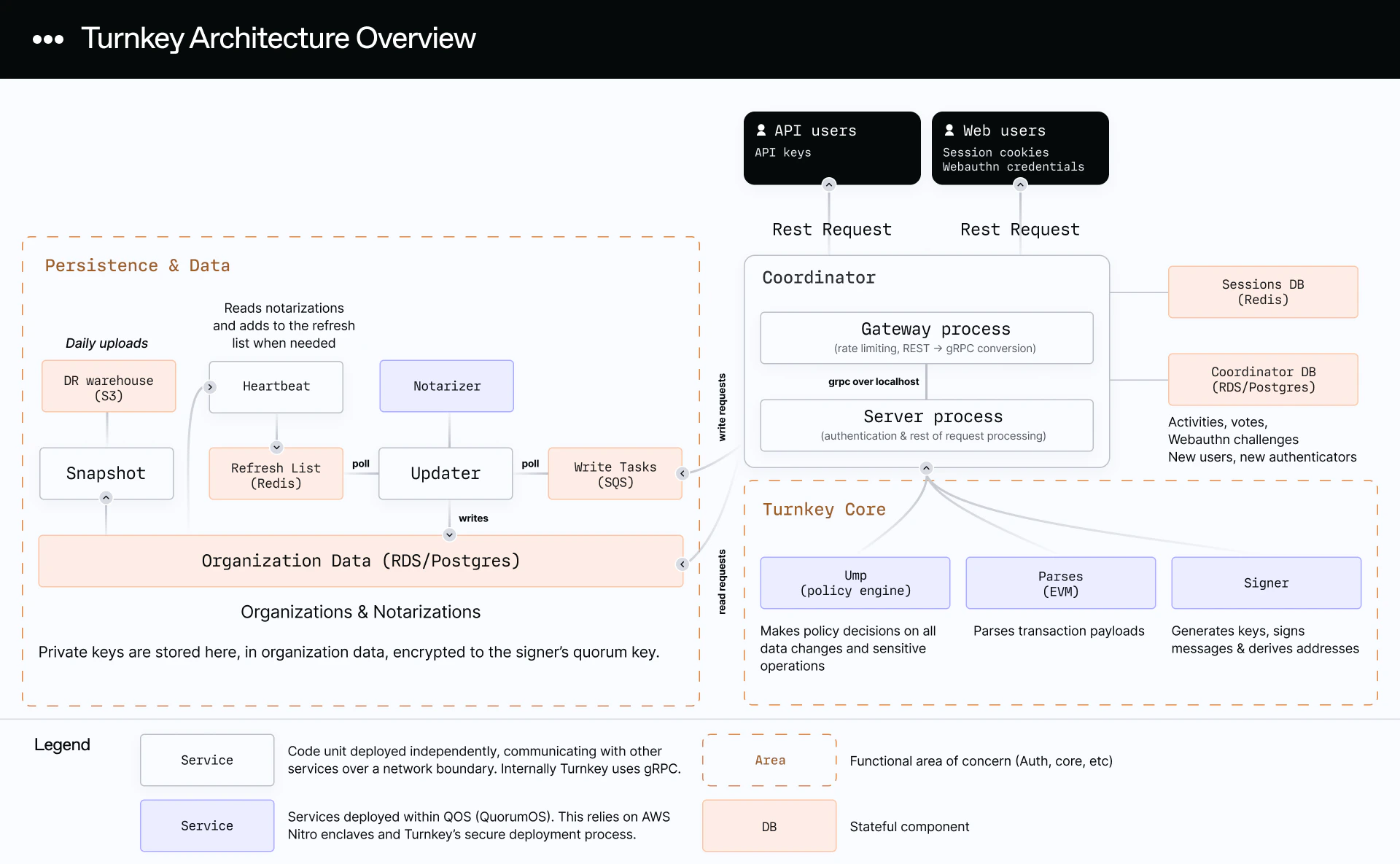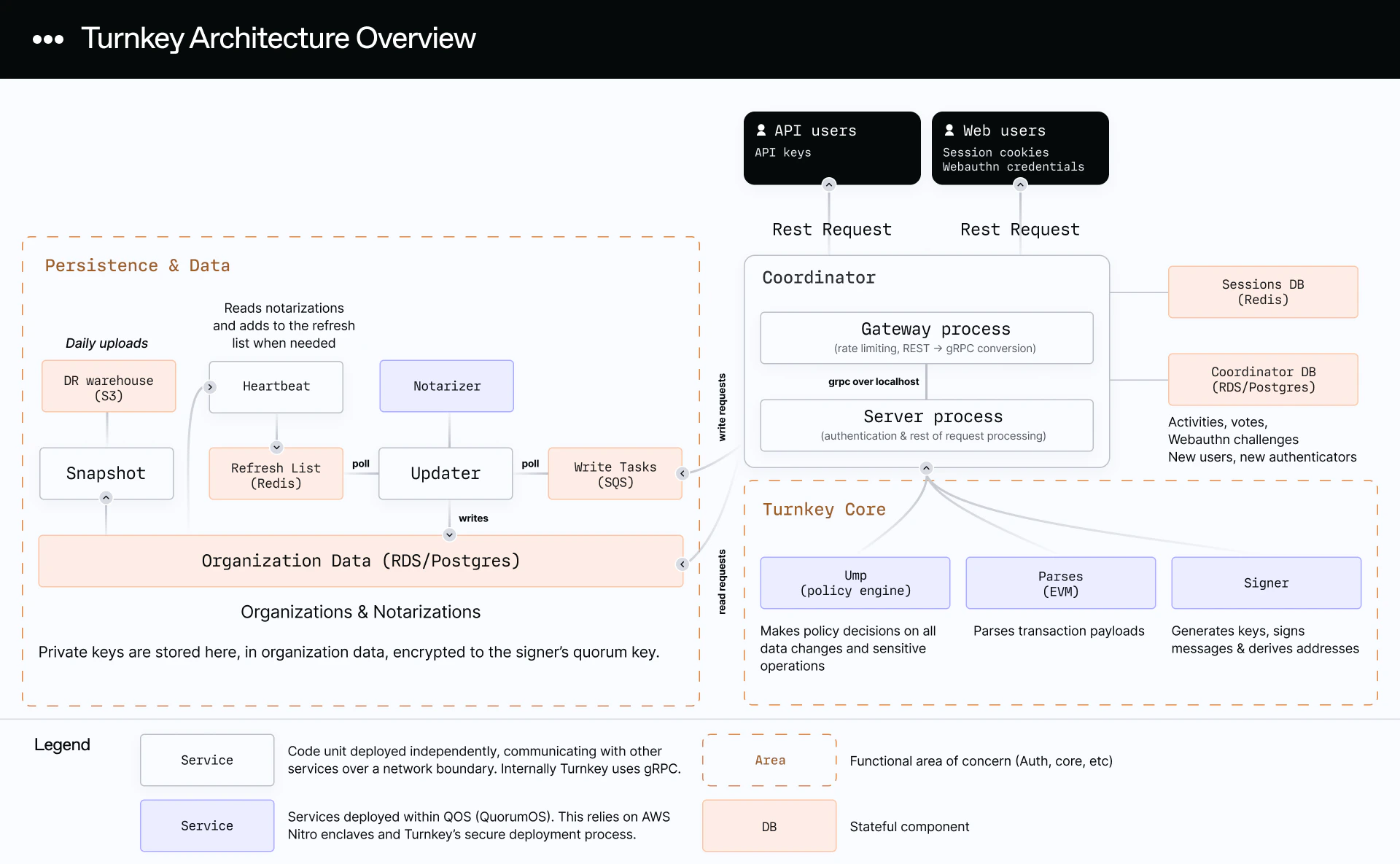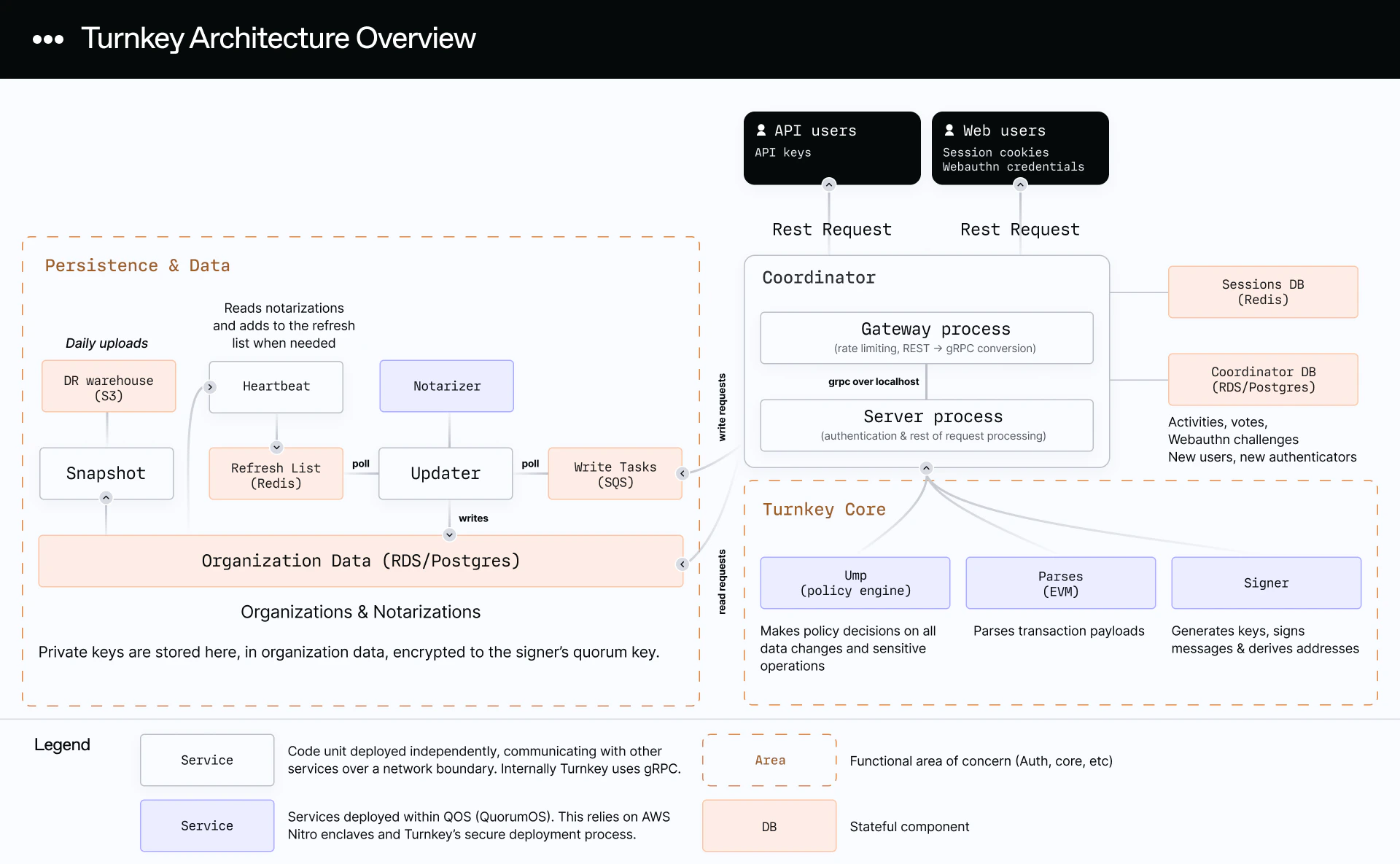
Architecture
Verifiable data
Enclave applications in Turnkey’s infrastructure are stateless, meaning there is no persistent data held behind the enclave boundary. Instead, data is stored in a PostgreSQL instance in our primary AWS account. Before any enclave application operates on account data, it first verifies that the data has been recently notarized by Turnkey’s notarizer. A recent stamp could be the result of an update or be initiated by the heartbeat service.
By verifying the authenticity of data using cryptographic signatures (no passwords!) and timestamping, we enable zero-risk data sharing between these apps and block man-in-the-middle or downgrade attacks. The combination of these features results in a system and an audit trail that is verifiable end-to-end.
The entire Turnkey architecture including this verifiable data flow is described below: