TLDR: what are passkeys?
From a technical point of view, passkeys are cryptographic key pairs created on end-user devices. Apple and Google have done a great job making these key pairs usable:- Key generation happens in secure end-user hardware.
- Using passkeys is easy thanks to native browser UIs and cross-device syncing.
- Passkey recovery for users is supported natively by Apple via iCloud Keychain and Google via the Google Password Manager.
- Access to passkeys is gated with OS-level biometrics: faceID, touchID, lock screen patterns, and so on.
- Passkeys are bound to the web domain that creates them. This is important to thwart phishing attacks, where an attacker hosts a similar-looking website to steal user credentials. This is doable with passwords; impossible with passkeys.
- Because passkeys rely on public key cryptography, passkeys have two components: a public key and a private key. Private keys are never disclosed to websites or apps, making them a lot harder to steal. Only public keys are sent. To authenticate, passkeys sign messages (with their private keys) and provide signatures as proofs, similar to crypto wallets.
Isn’t this similar to WebAuthn?
If you know about Webauthn, congratulations: a lot of this will feel familiar. Passkeys rely on the same web standard and the same browser APIs:navigator.credentials.create and navigator.credentials.get.
The difference? Passkeys are resident credentials and they can be synced between devices. As a result, they are not device-bound and can be used from any device.
How do cross-device syncing and recovery work?
Synchronization and recovery are both supported natively by Apple and Google:- With Apple, Passkeys created on one device are synced through iCloud Keychain as long as the user is logged in with their Apple ID. Apple covers both syncing and recovery in “About the security of passkeys”. For some additional detail, see this Q&A with the passkey team. Apple’s account recovery process is documented in this support page.
- With Google, Google Password Manager syncs passkeys across devices seamlessly. Google has plans to support syncing more broadly across different operating systems, see this support summary. Recovery is covered in this FAQ (“What happens if a user loses their device?”): it relies on Google’s overall account recovery process because passkeys are attached to Google accounts.
OS and browser support
Modern browsers have great support for passkeys. See caniuse for detailed information. Support also varies by operating system: this matrix has detailed information about OS-level support.Betting on WebAuthn and Passkeys
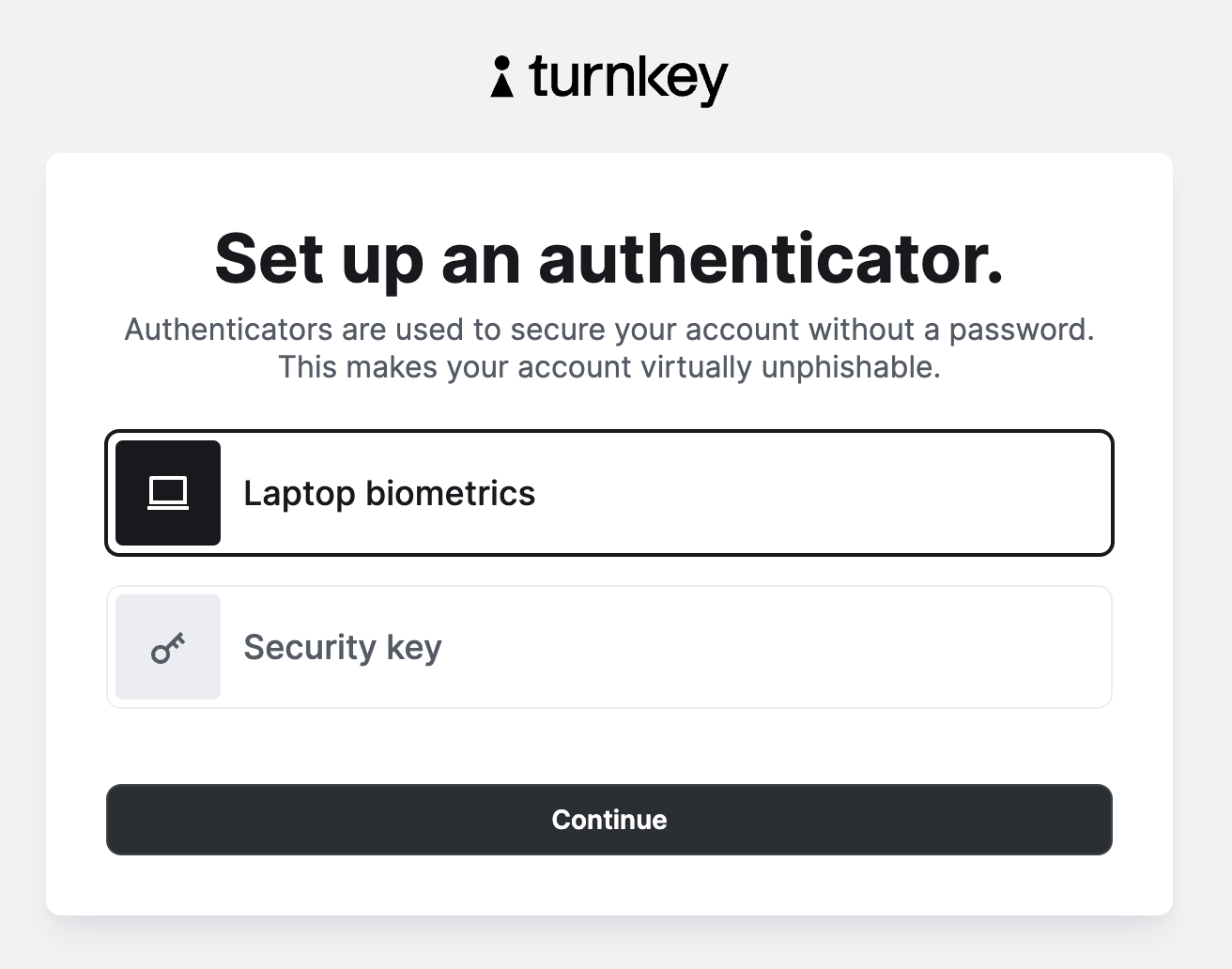
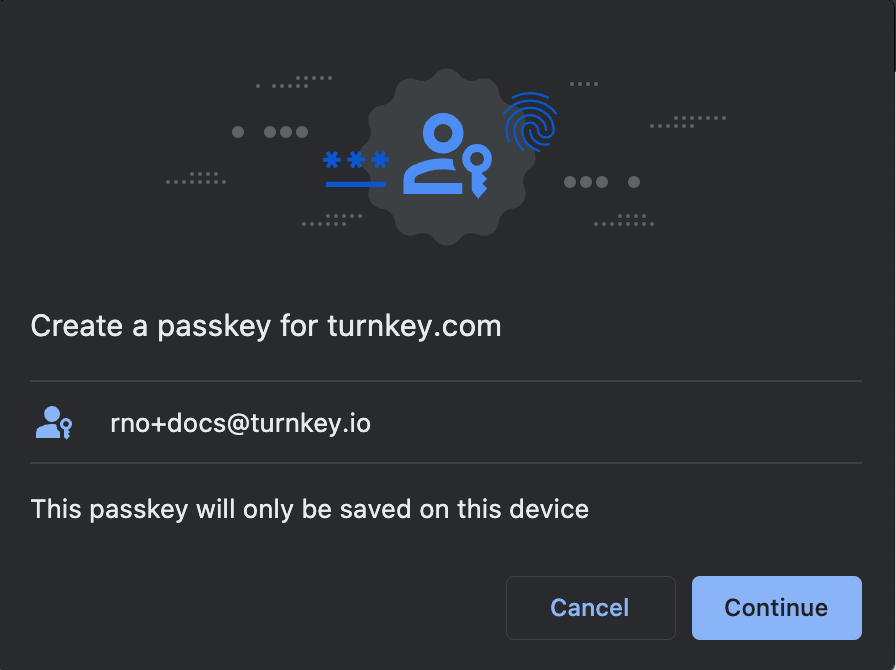
We believe it’s time to move away from passwords so we’ve built Turnkey without them. When you authenticate to Turnkey you’ll be prompted to create a new passkey: